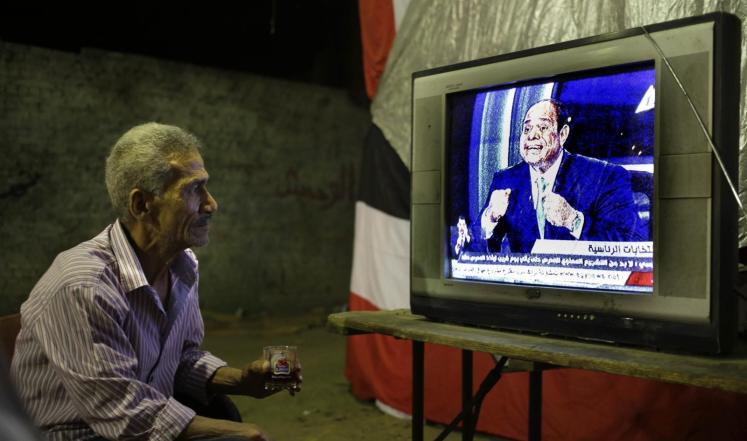
A month ago, the Egyptian Presidential Media Office announced the activation of the email address [email protected], through which the Egyptian people can communicate their inquiries and concerns directly to the Presidential Office. An official statement added that this comes within the framework of President Abdel Fattah El-Sisi’s keenness to directly communicate with the citizens, a matter he finds core to ensuring transparency and public participation in the decision making process.
A genuine initiative as it may seem, it clearly lacked the technical proficiency and online security expected of a presidential office. Besides the influx of thousands of messages received solely on the first day, the community interaction took an unexpected turn when the email server was made available for public use.
A website entitled ‘إبعت إيميلات من مكتب رئيس الجمهورية’ (Send e-mails from the Presidential Office) has been created by an anonymous developer who found out that the email server configuration lacks any authentication for use. Accordingly, anyone can access the email server and utilize it to their personal use through a simple tool available on the aforementioned website.
Needless to say, a tool exposing a fatal computing mistake such as this would inevitably spread like wildfire.
In the website, the developer explains that the e-mail address is an open mail relay, which is a Simple Mail Transfer Protocol (SMTP) server, configured in such a way that allows anyone on the Internet to send emails through it.
Although this used to be the default configuration in many mail servers when the Internet was initially setup, open mail relays have become unpopular because of their exploitation by spammers and worms. Many relays have been closed or placed on blacklists by other servers.
Practically speaking, an open mail relay cannot be hacked simply because the server doesn’t have any layers of security to hack through. It’s wide open!
The developer adds that this method is as good as extinct. The only mention of open mail relays takes place as standard knowledge for anyone working in the field of information technology (IT).
What may be considered as a primitive IT mistake was quickly remedied by shutting down the server op.gov.eg.
In a time when the easiest way to abuse a government is by hacking into its online system and retrieving confidential information and communication threads, it may be quite advisable to reevaluate the IT applications used by the Egyptian Presidential Office.







Comment (1)
I guess such challenge could be resolved via VPN like most of the businesses are doing now a days to remain protected from the security threats.
Business VPN by PureVPN is the most powerful against online privacy and security threats.